Between 2017 and 2023, North Korean hackers stole $3 billion in cryptocurrency. That’s not a typo. That’s more than the GDP of some small countries. And in 2024 alone, they stole $1.34 billion - more than double what they took the year before. Then, in February 2025, they pulled off the biggest heist in crypto history: $1.5 billion from Bybit, mostly in Ether. This wasn’t luck. It wasn’t a glitch. It was a state-run operation, carefully planned, patiently executed, and relentlessly repeated.
Who’s Behind It?
The hackers aren’t lone wolves. They’re part of North Korea’s military intelligence units, operating under names like Lazarus, TraderTraitor, and Slow Pisces. These aren’t random groups. They’re branches of a national cyberwarfare program. Their mission? Break sanctions. Fund nukes. Keep the regime running when traditional money flows dry up. The UN’s December 2024 report confirmed it: North Korea is the world’s most active state-sponsored crypto thief. They’ve carried out 58 major attacks since 2017. And they’re getting better. In 2024, they accounted for 61% of all crypto stolen globally - even though they only made up 20% of the total number of attacks. That means each of their heists is bigger, smarter, and more damaging than others.How They Do It: The LinkedIn Trap
Forget hacking servers with brute force. North Korea’s favorite trick? Social engineering. They target real people - employees at crypto companies - with fake job offers. In May 2024, they stole $308 million from DMM, a Japanese crypto platform. How? They posed as recruiters on LinkedIn. They reached out to engineers at Ginco, a company that builds wallet software for businesses. One employee, thinking they were applying for a new job, downloaded a Python script labeled "pre-employment test." It was malware. That one file gave them access to Ginco’s internal systems. Over the next two months, they watched. They waited. They studied how employees logged in, how transactions were approved, how communications flowed. Then, in mid-May, they hijacked a legitimate transaction request. A DMM employee asked to send funds. The hackers changed the destination address. $308 million vanished. This wasn’t a one-time trick. It’s their standard playbook: find a weak human, not a weak server. Train a target. Build trust. Wait. Strike when no one’s looking.The Bybit Heist: A New Level of Scale
The February 2025 attack on Bybit changed everything. $1.5 billion. In one go. More than all the thefts in 2024 combined. Chainalysis, the top blockchain intelligence firm, traced the stolen Ether through dozens of wallets. The hackers didn’t just cash out. They laundered it. They used decentralized exchanges. They swapped Ether for Bitcoin. They moved money across chains - Ethereum, Binance Chain, Solana - to confuse investigators. They split the cash into hundreds of tiny wallets, each holding just enough to avoid suspicion. This wasn’t chaos. It was precision. The same group that hit Ginco in May 2024 was behind this. They didn’t need to break into Bybit’s core systems. They didn’t need to crack passwords. They found a backdoor - a forgotten API key, a misconfigured smart contract, or a compromised employee. The details are still under investigation, but the pattern is clear: they’re no longer trying to break in. They’re waiting for you to open the door.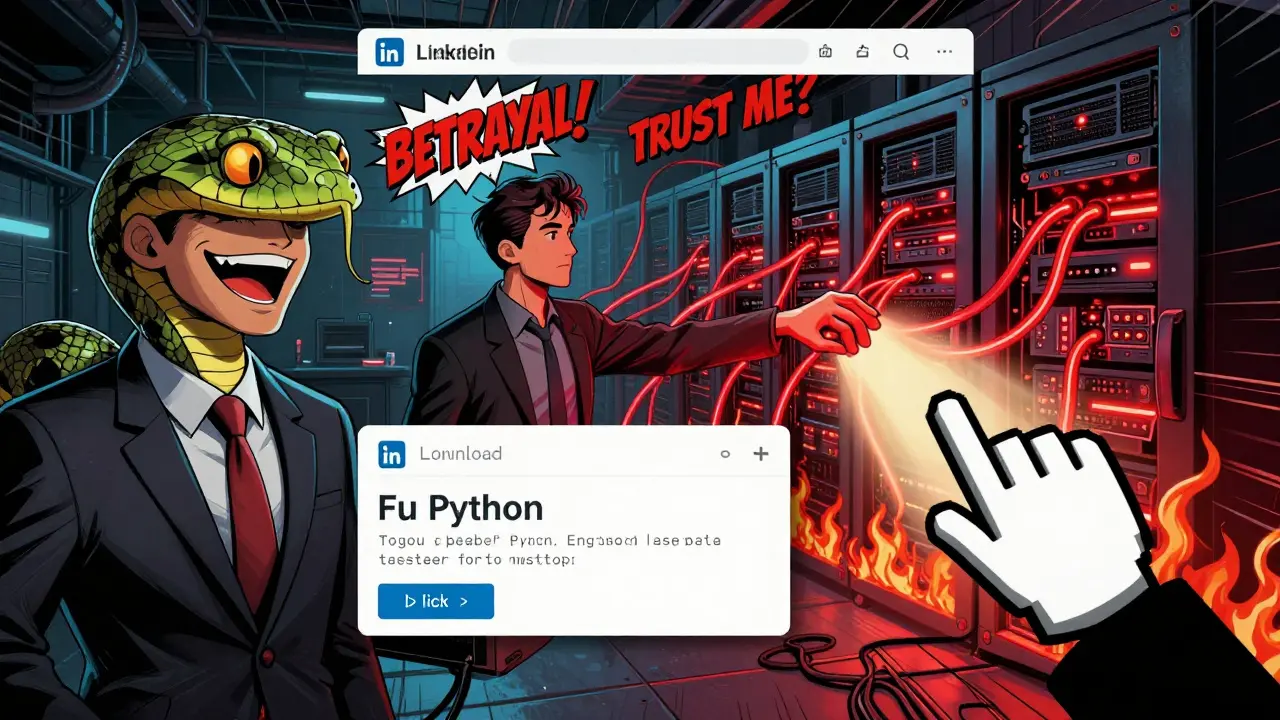
Why Crypto Exchanges Keep Getting Hit
Most crypto platforms think security is about firewalls and encryption. That’s not enough. North Korean hackers don’t care about your 2FA. They don’t care if you use cold storage. They care about your HR department. Your onboarding process. Your third-party contractors. Your intern who uses the same password for LinkedIn and your company’s admin panel. In 2024, over 80% of major crypto thefts started with a single employee being tricked. Not hacked. Tricked. A phishing email. A fake job interview. A LinkedIn message that looked real. That’s why even the biggest exchanges - Coinbase, Binance, Bybit - are still vulnerable. Their tech is strong. Their people are the weak link. And the attackers know it.What Happens to the Stolen Money?
This isn’t about getting rich. It’s about survival. North Korea’s economy is crushed under sanctions. They can’t sell oil. They can’t import tech. They can’t trade freely. So they turn to crypto. Every dollar stolen goes straight to funding their weapons programs - missiles, nuclear bombs, drones. The U.S. Treasury and the FBI have linked stolen funds to Pyongyang’s missile tests. The money doesn’t go into bank accounts. It goes into underground labs. Into testing sites. Into factories hidden in mountains. That’s why governments are treating this like a national security threat - not just a crime. When a hacker steals $1.5 billion, they’re not just stealing from an exchange. They’re funding a regime that threatens global stability.
Are You Safe? What You Can Do
If you’re a regular crypto user, you’re probably not at risk. But if you work for a crypto company - even a small one - your security needs to change. Here’s what actually works:- Train everyone - not just devs. HR, support, interns. Everyone gets phishing drills.
- Limit access - if you don’t need to touch a wallet, you shouldn’t have access to it.
- Use multi-sig wallets - no single person can move funds. Requires 3 out of 5 approvals.
- Monitor unusual activity - if a wallet sends funds to a new, unknown address, block it.
- Don’t trust GitHub links - never run code from a job applicant. Ever.
The Bigger Picture
Crypto was supposed to be decentralized. Untraceable. Free from governments. Instead, it’s become the new battlefield. North Korea turned blockchain technology - designed for transparency - into a tool for secrecy. They used public ledgers to hide their tracks. They turned open-source tools into weapons. They made crypto itself the target. The $3 billion stolen before 2024 was bad. The $1.5 billion stolen in February 2025 was a warning. And if nothing changes, the next heist will be even bigger. This isn’t just about hackers. It’s about how we build systems. Who we trust. What we ignore. The next time someone sends you a "simple test" from a recruiter, ask: What’s really on the other end?How did North Korea steal so much crypto without getting caught?
North Korean hackers avoid detection by using sophisticated laundering techniques. They move stolen funds across multiple blockchains, use decentralized exchanges, and split money into hundreds of small wallets. They also target human error - not system flaws - making it harder to trace back to a single point of failure. Attribution takes months, and by then, the money is already converted into cash or used to fund weapons programs.
Is Bitcoin or Ethereum more at risk from these attacks?
Ethereum has been the primary target because it supports smart contracts and decentralized finance (DeFi) platforms, which are easier to exploit through API vulnerabilities and wallet misconfigurations. The February 2025 Bybit heist stole $1.5 billion in Ether, showing that high-value DeFi systems are the most attractive targets. Bitcoin is harder to steal directly because it’s less flexible, but it’s often used as a laundering tool - stolen Ether is swapped for Bitcoin to obscure the trail.
Why do North Korean hackers use LinkedIn and fake job offers?
LinkedIn is trusted by professionals worldwide. It’s a goldmine for finding employees who have access to internal systems. By posing as recruiters, North Korean hackers build credibility over weeks or months. They ask for "code samples" or "tests" - which are actually malware. Once inside, they study workflows, steal session cookies, and wait for the perfect moment to move funds - often months after the initial contact.
Has any country successfully stopped a North Korean crypto heist?
No major heist has been stopped before it happened. However, after the 2024 DMM theft, the FBI, Japan’s National Police Agency, and Chainalysis worked together to freeze over $200 million in linked wallets. While they couldn’t recover all the money, they disrupted the laundering pipeline and exposed key wallet addresses used by Lazarus. This has led to increased monitoring by exchanges and stricter KYC rules for crypto-to-fiat conversions.
Are crypto exchanges improving their security?
Yes, but too slowly. Many now use multi-signature wallets, conduct regular employee training, and monitor blockchain activity in real time. However, most still focus on technical defenses - like encryption and firewalls - while ignoring human risk. The biggest improvements have come from exchanges that treat social engineering like a real threat: running mock phishing campaigns, limiting access rights, and auditing third-party vendors. But these practices aren’t industry-wide yet.


 Cryptocurrency Guides
Cryptocurrency Guides
Jeremy buttoncollector
February 21, 2026 AT 21:28So we’re just gonna keep letting NK turn blockchain into a covert ops playground? The real tragedy isn’t the $3B-it’s that we’re still treating this like a cybersecurity issue instead of a geopolitical war. We need sanctions on the devs who build the tools they exploit. Not just the wallets. The *infrastructure*.
And stop calling it 'social engineering.' That’s just corporate PR speak for 'we trained our interns to click anything that looks like a job offer.' It’s state-sponsored manipulation. Call it what it is.
Michelle Xu
February 22, 2026 AT 23:39As someone who works in crypto compliance, I’ve seen this play out too many times. The LinkedIn tactic is terrifyingly effective because it preys on ambition-not greed. Engineers want to grow. They want to move up. And NK’s recruiters offer them a path… with malware disguised as a portfolio review.
Multi-sig wallets help, but they’re useless if HR approves a fake candidate with admin access. We need mandatory behavioral audits for every hire, not just background checks. And yes, this applies to interns too.
Amanda Markwick
February 23, 2026 AT 21:38Let’s not forget the real hero here: the guy who didn’t click the link.
I’ve worked at three startups. Two got hit. The third? One junior dev said, 'This feels off.' He didn’t know why. He just trusted his gut. That’s the real security layer. Not firewalls. Not 2FA. Human intuition.
Maybe we should stop training people to be 'secure' and start training them to be suspicious. Not paranoid. Suspicious. Like a cat that won’t sit on a new blanket.
Also-why are we still using GitHub links from applicants? That’s like letting someone into your house because they sent you a resume in a nice font.
Sriharsha Majety
February 24, 2026 AT 00:18Neeti Sharma
February 24, 2026 AT 17:34Fiona Monroe
February 26, 2026 AT 16:23It is imperative to recognize that the systemic vulnerability lies not in cryptographic protocols, but in organizational culture. The persistence of credential reuse, unvetted third-party integrations, and the normalization of 'quick fixes' in engineering workflows renders even the most robust technical controls obsolete.
Until HR, legal, and security functions operate as a unified triad-with shared KPIs and mandatory cross-training-we are merely rearranging deck chairs on the Titanic.
Lucy Simmonds
February 27, 2026 AT 18:02Maggie House
February 28, 2026 AT 15:40Dana Sikand
March 1, 2026 AT 17:18Okay I’m crying. I work in DevOps at a small exchange. We had a recruiter DM our lead dev on LinkedIn last month. He almost took it. He said the offer looked legit-good grammar, real company profile, even had a Zoom call scheduled.
We caught it because our intern noticed the email domain was 'ginc0.com' not 'ginco.com'. One zero. One. Freaking. Letter.
Now we have a 'fake recruiter Friday' where we send fake job posts to the whole team. It’s weird. It’s fun. It’s saving our bacon.
Also-stop trusting GitHub. Ever. I’ve seen devs run scripts from strangers. I’ve seen them say 'it’s just a test.' NO. IT’S NOT.
Elizabeth Smith
March 2, 2026 AT 10:26If you’re not outraged by this, you’re complicit. We’ve built a financial system where the most vulnerable people-those trying to climb the ladder-are the ones targeted. The hackers don’t care about your blockchain. They care about your dreams.
And we let them. We let them because we value efficiency over ethics. We let them because we don’t train people to question. We train them to comply.
It’s not a hack. It’s a moral failure.
Robert Kromberg
March 3, 2026 AT 17:06Maybe instead of blaming NK, we should ask why we’re so easy to manipulate. Why do we trust job offers from strangers? Why do we download code without checking? Why do we think 'it won’t happen to me'?
I’m not saying we should stop being open. But maybe we need to be more thoughtful. Not paranoid. Thoughtful.
Also-has anyone considered that the real vulnerability is in how we teach people to use tech? Not the tech itself?
Curtis Dunnett-Jones
March 5, 2026 AT 15:46It is an undeniable fact that the current paradigm of cybersecurity is fundamentally flawed. The emphasis on perimeter defense ignores the human layer, which is not a vulnerability-it is the primary attack surface.
Organizations must institutionalize adversarial simulations, not as annual exercises, but as continuous, embedded cultural practices. The notion of 'security awareness training' as a checkbox is an anachronism. We require behavioral conditioning, not education.
Felicia Eriksson
March 6, 2026 AT 12:29Patrick Streeb
March 8, 2026 AT 03:36While the geopolitical implications are significant, the operational lesson is universal: trust is the most dangerous permission. The fact that a single employee’s trust in a recruiter led to a $1.5 billion breach speaks to a deeper institutional failure in verification protocols.
It is not enough to train users. We must redesign systems to assume human error-not as a failure, but as a constant.
Tracy Whetsel
March 9, 2026 AT 16:00Hey everyone, just wanted to say-this is why I started doing monthly 'fake phishing' games with my team. We send silly emails like 'URGENT: Your Slack password expires in 5 min!' and the person who clicks gets a cookie. 😄
It’s not about scaring people. It’s about making security fun. We’ve cut our incident rate by 70% in 6 months.
You don’t need fancy tech. You need a culture that says: 'It’s okay to pause. It’s okay to ask.'
And hey-if you’re reading this, send me a DM. I’ll send you our free phishing quiz. No strings. Just love. 💛
Cathy Sunshine
March 10, 2026 AT 06:07Of course it’s happening. The entire crypto industry is a Ponzi scheme built on the delusion that 'decentralized' means 'secure.' They didn’t steal $3 billion-they exposed the entire system’s bankruptcy.
The real crime? We still treat blockchain as if it’s magic. It’s code. It’s written by humans. And humans are weak.
Stop romanticizing decentralization. Start auditing people.
Dee Resin
March 10, 2026 AT 08:54Tanvi Atal
March 12, 2026 AT 05:06Colin Lethem
March 12, 2026 AT 05:28Kristi Emens
March 13, 2026 AT 15:43It’s not about the hackers. It’s about us.
Kaitlyn Clark
March 14, 2026 AT 02:10ok but can we talk about how wild it is that they use linkedin?? like… of all places??
i just got a job offer from a 'crypto startup' on linkedin last week. i was like 'wait… is this real??' then i checked the domain-'ginc0.com'-and i was like 'ohhhhhhh nope.'
we need a 'this is fake' button on linkedin. like a 'report' button but for 'this recruiter is trying to steal my life savings.'
also… i just told my whole team about this. we’re all doing a fake test today. send help. or cookies. 🍪